Vulnerability
Vulnerability
|
  90052
90052 |
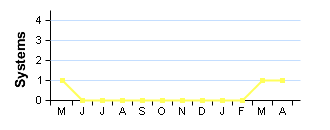
Administration Interface with Weak Password

|
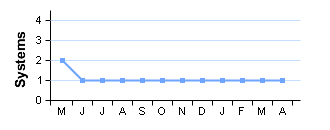
 1 System 1 System |
High Risk |
|---|
| Description | This host is exposing an administration interface to the Internet with a default or easily guessable password. This allows a remote attacker full access to modify settings or content. The login details are: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Set a stronger password and/or ensure this interface is not accessible from the Internet. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-1999-0508 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | |||
| Systems |
www.your_company.nl (192.168.0.103)


|
|---|
 Vulnerability
Vulnerability
|
  10993
10993 |
IIS ASP.NET Application Trace Enabled

|
 1 System 1 System |
High Risk |
|---|
| Description | This web server has an ASP.NET application running with application tracing enabled. This allows an attacker to view detailed information on recent HTTP requests. Sensitive information revealed includes physical paths and even session IDs. An example URL you can use to exploit this is: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Set 'trace enabled=false' in web.config | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | ASP.Net Tracing Overview Tracing How to: Enable Tracing for an ASP.NET Page How to: Enable Tracing for an ASP.NET Application | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.your_company.nl (192.168.0.103)


|
|---|
 Vulnerability
Vulnerability
|
  90027
90027 |
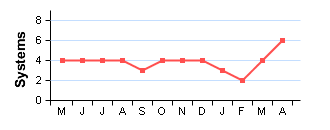
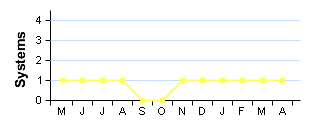
High Risk Ports Open |
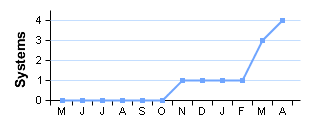
 6 Systems 6 Systems |
High Risk |
|---|
| Description | The following high risk ports are open: [For specific url or description click server link below.] Note: Even if the ports are immediately closed after being opened, this is still a security risk as packets are reaching the destination host. It is recommended to completely drop packets from untrusted sources instead. |
||||
|---|---|---|---|---|---|
| Solution | Ensure that the ports are filtered by your router or firewall or close the ports on the affected systems. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 6.4 (Medium) (AV:N/AC:L/Au:N/C:P/I:P/A:N) | |||
| Systems |
dns0.example.com (192.168.0.110)
 [Oct 2014]
[Oct 2014]
|
sql1.manc.yourcompany.com (192.168.1.52)
 [Feb 2015]
[Feb 2015]
|
|---|---|---|
sql2.manc.yourcompany.com (192.168.1.53)
 [Nov 2014]
[Nov 2014]
|
www.your_company.fr (192.168.0.105)


| |
www.your_company.nl (192.168.0.103)


|
www.yourcompany.com (192.168.0.101)


| |
 Vulnerability
Vulnerability
|
  10264
10264 |
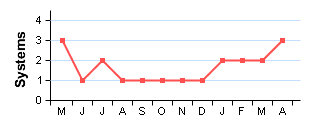
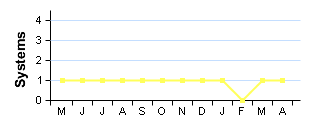
SNMP Default Community Names |
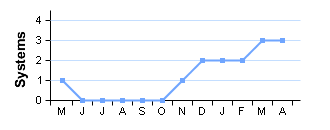
 3 Systems 3 Systems |
High Risk |
|---|
| Description | This system is running an SNMP agent which uses an easily guessable community string. This enables an attacker to extract a large amount of useful information. If a writeable community string is guessable, an attacker could make configuration changes to the server. Here is a sample of the information that can be extracted: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Disable SNMP, or change the community string to something unguessable. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-1999-0186 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | |||
| CVE-1999-0254 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-1999-0516 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-1999-0517 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-2004-0311 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-2004-1474 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:P/A:N) | ||||
| CVE-2010-1574 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| Systems |
dns0.example.com (192.168.0.110)
 [Feb 2015]
[Feb 2015]
|
www.your_company.fr (192.168.0.105)


|
|---|---|---|
www.your_company.nl (192.168.0.103)
 [Jul 2014]
[Jul 2014]
|
 Vulnerability
Vulnerability
|
  10882
10882 |
SSH Protocol Version 1 Enabled |
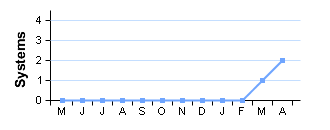
 2 Systems 2 Systems |
High Risk |
|---|
| Description | This system is running an SSH service with SSH protocol version 1 enabled. This version of the protocols is not completely cryptographically secure. A passive eavesdropper could use these weaknesses to extract information such as the lengths of passwords and commands. | ||||
|---|---|---|---|---|---|
| Solution | Configure your SSH service to only use protocol version 2. For OpenSSH, set the 'Protocol' option to '2'. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | US-CERT VU#596827 OSVDB ID 2116 | ||||
| CVE References | CVE-2001-0361 | CVSS2 4.0 (Medium) (AV:N/AC:H/Au:N/C:P/I:P/A:N) | |||
| CVE-2001-0572 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-2001-1473 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| Systems |
mail.example.com (192.168.0.111)
 [Nov 2014]
[Nov 2014]
|
www.yourcompany.net (192.168.0.102)
 [Jan 2015]
[Jan 2015]
|
|---|---|---|
 Vulnerability
Vulnerability
|
  11030
11030 |
Apache < 1.3.26 Chunked Encoding Vulnerability |
 1 System 1 System |
High Risk |
|---|
| Description | This system is running a vulnerable version of Apache, according to its banner. There is a buffer overrun vulnerability in code related to chunked encoding. A remote attacker could use this to crash the service and may be able to take control of the system. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Apache Security Bulletin 20020620 CERT Advisory CA-2002-17 Bugtraq ID 5033 US-CERT VU#944335 Apache 1.3 Changelog | ||||
| CVE Reference | CVE-2002-0392 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | |||
| Systems |
www.example.com (192.168.0.112)
 [Oct 2014]
[Oct 2014]
|
|---|
 Vulnerability
Vulnerability
|
  10605
10605 |
BIND < 8.2.3 Buffer Overrun

|
 1 System 1 System |
High Risk |
|---|
| Description | This system is running a vulnerable version of BIND, according to its banner. There is a buffer overrun vulnerability in code related to transaction signatures (TSIG). A remote attacker could use this to crash the service and take control of the system. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-2001-0010 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | |||
| CVE-2001-0011 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-2001-0012 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | ||||
| CVE-2001-0013 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| Deadline | 13 August 2014 | ||||
| Systems |
dns0.example.com (192.168.0.110)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  11424
11424 |
IIS WebDAV Buffer Overrun |
 1 System 1 System |
High Risk |
|---|
| Description | This system is an IIS server running WebDAV. This may be vulnerable to a buffer overrun when a malicious WebDAV request is sent. When running on an unpatched Windows NT4, Windows 2000, or Windows XP; an attacker could use this to crash the service or take control of the system. Note: This may be a false positive as it is not possible to determine remotely if the patch has been applied. |
||||
|---|---|---|---|---|---|
| Solution | Apply the patch from Microsoft. In addition we suggest you edit registry to disable WebDAV, following these instructions. If you do not disable WebDAV then this vulnerability will continue appearing until you stoplist it. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Microsoft Security Bulletin MS03-007 CERT Advisory CA-2003-09 Microsoft Knowledge Base Q241520 | ||||
| CVE Reference | CVE-2003-0109 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | |||
| Systems |
www.your_company.nl (192.168.0.103)
 [May 2014]
[May 2014]
|
|---|
 Vulnerability
Vulnerability
|
  10481
10481 |
MySQL Database Accessible Without Password

|
 1 System 1 System |
High Risk |
|---|
| Description | This system is running a MySQL service that allows network connections with no password. A remote attacker could use this to manipulate the database in any way. The unpassworded accounts are: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Add a password or restrict access to trusted addresses. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Bugtraq ID 11704 | ||||
| CVE References | CVE-2002-1809 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | |||
| CVE-2004-1532 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| Deadline | 01 April 2015 | ||||
| Systems |
sql1.manc.yourcompany.com (192.168.1.52)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  11316
11316 |
Sendmail < 8.12.8 Buffer Overrun

|
 1 System 1 System |
High Risk |
|---|
| Description | This system is running a vulnerable version of Sendmail, according to its banner. There is a buffer overrun vulnerability in code related to message header parsing. A remote attacker could use this to crash the service or possibly take control of the system. This version may also be vulnerable to a flaw in smrsh which allows local users to escalate their privileges. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | US-CERT VU#398025 | ||||
| CVE References | CVE-2001-1349 | CVSS2 3.7 (Low) (AV:L/AC:H/Au:N/C:P/I:P/A:P) | |||
| CVE-2002-1165 | CVSS2 4.6 (Medium) (AV:L/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-2002-1337 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| Deadline | 01 May 2015 | ||||
| Systems |
mail.example.com (192.168.0.111)
 [May 2014]
[May 2014]
|
|---|
 Vulnerability
Vulnerability
|
  90068
90068 |
SSL Certificate Problems

|
 1 System 1 System |
Medium Risk |
|---|
| Description | This system has presented a certificate that does not meet the requirements for establishing a secure session. The problems detected were: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Ensure you have a valid certificate issued by a trusted certificate authority. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Wildcard Certificates Public Key Certificates X.509 Certificate Authorities | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 4.3 (Medium) (AV:N/AC:M/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.example.com (192.168.0.112)


|
|---|
 Vulnerability
Vulnerability
|
  10539
10539 |
Globally Useable Name Server |
 3 Systems 3 Systems |
Medium Risk |
|---|
| Description | This system is running a name server that allows any system on the Internet to perform recursive queries and resolve third-party domain names. An attacker could use this to extract information about your name lookup patterns, and may be able to perform DNS cache poisoning attacks. | ||||
|---|---|---|---|---|---|
| Solution | Restrict recursive queries to trusted addresses. For servers running BIND, use the allow-recursion or allow-query directives. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Securing Windows Server 2003 Domain Controllers Disabling recursion in BIND | ||||
| CVE Reference | CVE-1999-0024 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:P/A:N) | |||
| Systems |
www.your_company.fr (192.168.0.105)


|
www.your_company.nl (192.168.0.103)


|
|---|---|---|
www.yourcompany.net (192.168.0.102)
 [May 2014]
[May 2014]
|
 Vulnerability
Vulnerability
|
  11137
11137 |
Apache < 1.3.27 Multiple Vulnerabilities |
 2 Systems 2 Systems |
Medium Risk |
|---|
| Description | This system is running a vulnerable version of Apache, according to its banner. There is a cross-site scripting vulnerability through the Host: header, if UseCanonicalName is Off. Exploitation is only possible where wildcard DNS is used. There is also a buffer overrun in the ApacheBench module - if this is enabled, it may allow arbitrary code execution. A further vulnerability exists in the shared memory scoreboard, but this is only exploitable by a local user. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. Workaround : Set UseCanonicalName to On and disable ApacheBench |
||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Apache 1.3 Changelog | ||||
| CVE References | CVE-2002-0839 | CVSS2 7.2 (High) (AV:L/AC:L/Au:N/C:C/I:C/A:C) | |||
| CVE-2002-0840 | CVSS2 6.8 (Medium) (AV:N/AC:M/Au:N/C:P/I:P/A:P) | ||||
| CVE-2002-0843 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| Systems |
www.example.com (192.168.0.112)
 [Oct 2014]
[Oct 2014]
|
www.yourcompany.co.uk (192.168.0.100)
 [Nov 2014]
[Nov 2014]
|
|---|---|---|
 Vulnerability
Vulnerability
|
  11378
11378 |
MySQL < 3.23.56 Privilege Escalation |
 2 Systems 2 Systems |
Medium Risk |
|---|
| Description | This system is running a vulnerable version of MySQL, according to its banner. There is insufficient permissions checking in code related to the "select into outfile" SQL command. A database user could use this to overwrite configuration files and escalate privileges. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Bugtraq ID 7052 | ||||
| CVE Reference | CVE-2003-0150 | CVSS2 9.0 (High) (AV:N/AC:L/Au:S/C:C/I:C/A:C) | |||
| Systems |
sql1.manc.yourcompany.com (192.168.1.52)
 [Feb 2015]
[Feb 2015]
|
sql2.manc.yourcompany.com (192.168.1.53)
 [Dec 2014]
[Dec 2014]
|
|---|---|---|
 Vulnerability
Vulnerability
|
  12280
12280 |
Apache < 1.3.31, 2.0.49 Multiple Vulnerabilities |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running a vulnerable version of Apache HTTP Server, according to its banner or fingerprint. It is possible for remote attackers to inject escape characters in the log files. A remote attacker can also cause a denial of service by making a long-lasting connection to a rarely used port. For Apache 1.x on 64-bit platforms, there is a mod_access weakness related to IP address rules without a netmask. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Buqtraq ID 9930 Buqtraq_9921 Buqtraq ID 9829 US-CERT VU#132110 Apache 2.0 Changelog Apache 1.3 Changelog | ||||
| CVE References | CVE-2003-0020 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:P/A:N) | |||
| CVE-2003-0993 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-2004-0174 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:N/A:P) | ||||
| Systems |
www.example.com (192.168.0.112)
 [Feb 2015]
[Feb 2015]
|
|---|
 Vulnerability
Vulnerability
|
  11039
11039 |
Apache mod_ssl < 2.8.10 off by one Vulnerability |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running a vulnerable version of the mod_ssl Apache module. There is an "off by one" buffer overrun in code related to parsing configuration. A local user with control over .htaccess files could use this to crash the service or take control of the system. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Securiteam advisory Bugtraq ID 5084 | ||||
| CVE Reference | CVE-2002-0653 | CVSS2 4.6 (Medium) (AV:L/AC:L/Au:N/C:P/I:P/A:P) | |||
| Systems |
www.example.com (192.168.0.112)
 [Oct 2014]
[Oct 2014]
|
|---|
 Vulnerability
Vulnerability
|
  10595
10595 |
DNS Zone Transfer

|
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running a name server that allows DNS zone transfers to be performed. This information could be useful to an attacker trying to map your network. The configuration may be intentional, but it's usual practice to restrict zone transfers. Here is a sample of the data that can be extracted: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Restrict zone transfers to trusted addresses, usually just your slave name servers | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-1999-0532 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Deadline | 13 February 2015 | ||||
| Systems |
dns0.example.com (192.168.0.110)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  10661
10661 |
IIS .printer ISAPI Filter Enabled |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running IIS and has the .printer ISAPI filter enabled. Some versions of this filter contain a buffer overrun vulnerability. A remote attacker could use this to crash the service or take control of the system. Note: To avoid crashing your server, we have not directly tested for the vulnerability and this may not be a real hole. However, as the filter is not usually required, you should turn it off as a matter of good practice. |
||||
|---|---|---|---|---|---|
| Solution | If you don't require this filter, disable it. If it is required, make sure the latest patches are applied. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Microsoft Security Bulletin MS01-023 | ||||
| CVE Reference | CVE-2001-0241 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | |||
| Systems |
www.your_company.nl (192.168.0.103)
 [Feb 2015]
[Feb 2015]
|
|---|
 Vulnerability
Vulnerability
|
  10991
10991 |
IIS global.asa Accessible |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running IIS and allows retrieval of the /global.asa file. This is a global configuation file which may contain sensitive information such as database passwords, physical paths and configuration options. This vulnerability may be caused by a missing ISAPI map of the .asa extension to asp.dll. Here is a sample of your global.asa file: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Restore the .asa map. Alternatively, use a filter program such as URLScan to explicity forbid such requests. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.your_company.nl (192.168.0.103)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  10629
10629 |
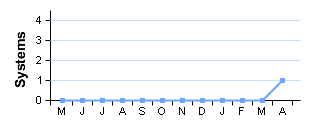
Lotus Domino Anonymous Database Access |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running Lotus Domino. Some databases are accessible without authentication: [For specific url or description click server link below.] This usually represents a security risk as the information contained is accessible to anyone on the internet.
|
||||
|---|---|---|---|---|---|
| Solution | Reconfigure Domino to require authentication for these databases. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-2000-0021 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| CVE-2002-0664 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| Systems |
www.yourcompany.com.my (192.168.0.106)
 [Feb 2015]
[Feb 2015]
|
|---|
 Vulnerability
Vulnerability
|
  11574
11574 |
OpenSSH < 3.6.1p2 PAM Timing Attack |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system appears to be running a vulnerable version of OpenSSH. If PAM authentication is used there is a timing attack against the protocol. A remote attacker could use this to conduct brute force attacks against users' passwords. Note: Tests for this vulnerability are sensitive to network conditions. This vulnerability may be a false positive. |
||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-2003-0190 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| CVE-2003-1562 | CVSS2 5.1 (Medium) (AV:N/AC:H/Au:N/C:P/I:P/A:P) | ||||
| Systems |
mail.example.com (192.168.0.111)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  12110
12110 |
OpenSSL < 0.9.6m, 0.9.7d SSL/TLS Handshake Denial of Service |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running a vulnerable version of OpenSSL, according to its banner. A null-pointer assignment in the do_change_cipher_spec() function and another flaw when using Kerberos ciphersuites could allow a remote attacker to crash the service using a specially crafted SSL/TLS handshakes. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | OpenSSL Security Advisory [17 March 2004] US-CERT VU#288574 US-CERT VU#465542 | ||||
| CVE References | CVE-2004-0079 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:N/A:P) | |||
| CVE-2004-0112 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:N/A:P) | ||||
| Systems |
apollo.example.com (192.168.0.81)
 [Nov 2014]
[Nov 2014]
|
|---|
 Vulnerability
Vulnerability
|
  10249
10249 |
SMTP Server Allows VRFY/EXPN |
 1 System 1 System |
Medium Risk |
|---|
| Description | This system is running an SMTP server which allows the VRFY and/or EXPN commands. These can be used to check the validity of accounts, find the delivery address of mail aliases, or even determine the full name of a recipient. An attacker could use this information to focus their attacks, or aid social engineering. The information leakage is unnecessary so you should disable these commands. | ||||
|---|---|---|---|---|---|
| Solution | If you are using sendmail, add the configuration directive 'PrivacyOptions=goaway'. For other mail daemons, consult the documentation. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | The VRFY and EXPN verbs RFC 2505 | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Systems |
mail.example.com (192.168.0.111)
 [Mar 2015]
[Mar 2015]
|
|---|
 Vulnerability
Vulnerability
|
  10884
10884 |
NTP Information Leakage

|
 1 System 1 System |
Low Risk |
|---|
| Description | This system is running an NTP server that responds to information requests. An attacker could use this to extract information about the system, e.g. operating system, upstream NTP server and detailed clock information. | ||||
|---|---|---|---|---|---|
| Solution | Configure ntpd to ignore information requests. Alternatively, use a firewall to restrict NTP to trusted addresses. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.yourcompany.com (192.168.0.101)


|
|---|
 Vulnerability
Vulnerability
|
  90001
90001 |
Holes Detected in Firewall Configuration |
 4 Systems 4 Systems |
Low Risk |
|---|
| Description | This system is protected by a firewall which blocks access to TCP ports in inconsistent ways. Incoming TCP connections to most ports are simply dropped, however some ports were discovered where the connection is actively refused, for example with a TCP RST. This often indicates a firewall configuration error, and commonly occurs when the configuration has not been altered in line with changing system configuration behind the firewall. For example when a service such as a mail server is removed, but the corresponding firewall rule is not. The TCP ports which actively refuse connections are: [For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Reconfigure your firewall to completely drop all connections on ports that you are not running services on. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Firewalls FAQ | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | |||
| Systems |
dns0.example.com (192.168.0.110)


|
mail.example.com (192.168.0.111)
 [Mar 2015]
[Mar 2015]
|
|---|---|---|
www.example.com (192.168.0.112)
 [Nov 2014]
[Nov 2014]
|
www.your_company.nl (192.168.0.103)
 [Mar 2015]
[Mar 2015]
| |
 Vulnerability
Vulnerability
|
  11213
11213 |
TRACE and/or TRACK Methods Enabled |
 3 Systems 3 Systems |
Low Risk |
|---|
| Description | This system supports the HTTP TRACE and/or TRACK methods. These increase the exploitability of any cross-site scripting vulnerabilities that may exist in your site. As they are primarily intended for debugging, they can be turned off without reduction of service. | ||||
|---|---|---|---|---|---|
| Solution | Disable these methods on production servers. Microsoft IIS 6 and IIS 7: Use the URLScan Security tool Microsoft IIS 5: Use the IIS Lockdown tool Apache httpd: Use mod_rewrite to redirect unallowed verbs to the forbidden target, or with newer versions use the configuration option 'TraceEnable off'. |
||||
| Category | Hosting or infrastructure flaw. | ||||
| References | US-CERT VU#867593 UrlScan Security Tool IIS Lockdown Tool Apache TraceEnable Directive | ||||
| CVE References | CVE-2003-1567 | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | |||
| CVE-2004-2320 | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | ||||
| CVE-2010-0386 | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | ||||
| Systems |
www.example.com (192.168.0.112)
 [Mar 2015]
[Mar 2015]
|
www.yourcompany.co.uk (192.168.0.100)
 [May 2014]
[May 2014]
|
|---|---|---|
www.yourcompany.net (192.168.0.102)
 [Dec 2014]
[Dec 2014]
|
 Vulnerability
Vulnerability
|
  12217
12217 |
DNS Cache Snooping |
 2 Systems 2 Systems |
Low Risk |
|---|
| Description | This system is running a DNS server that accepts queries from any address (although recursive queries may be disabled). The name server responds differently for domains that have recently been looked-up. An attacker could use this to determine if certain sites have been visited by users of this nameserver. | ||||
|---|---|---|---|---|---|
| Solution | Restrict access to DNS caches to local users. For Bind, use the "AllowQuery" directive. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | DNS Cache Snooping What is DNS Cache Snooping? | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 0.0 (Low) (AV:N/AC:M/Au:N/C:N/I:N/A:N) | |||
| Systems |
www.your_company.nl (192.168.0.103)


|
www.yourcompany.net (192.168.0.102)
 [Mar 2015]
[Mar 2015]
|
|---|---|---|
 Vulnerability
Vulnerability
|
  10077
10077 |
Microsoft Frontpage Extensions Installed |
 1 System 1 System |
Low Risk |
|---|
| Description | This system is running Microsoft Frontpage extensions. These have had a history of insecurity, so you should carefully check that you have the latest patches applied. It is also common for Frontpage extensions to be insecure because they are misconfigured.[For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | If you do not require Frontpage extensions, disable them. If they are required, make sure the latest patches are applied. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Microsoft Security Bulletin MS02-018 Microsoft Knowledge Base Q813379 Microsoft Knowledge Base Q813380 | ||||
| CVE Reference | CVE-2000-0114 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.your_company.nl (192.168.0.103)
 [May 2014]
[May 2014]
|
|---|
 Vulnerability
Vulnerability
|
  10759
10759 |
Private IP Address Leakage |
 1 System 1 System |
Low Risk |
|---|
| Description | This system exposes its RFC 1918 private IP address. This is the internal IP address of the system, that would usually be masked by a proxy or NAT firewall. This information may be useful to an attacker trying to remotely map your network or prepare an attack. The private IP address is:[For specific url or description click server link below.] |
||||
|---|---|---|---|---|---|
| Solution | Update your web server configuration. For IIS, issue "adsutil set w3svc/UseHostName True" and restart. On Apache, ensure that ServerName in httpd.conf is set to a hostname. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Bugtraq ID 1499 Microsoft Knowledge Base Q218180 RFC 1918 | ||||
| CVE Reference | CVE-2000-0649 | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | |||
| Systems |
www.yourcompany.co.uk (192.168.0.100)
 [Mar 2015]
[Mar 2015]
|
|---|