Criticality: 

| Groups and Contacts | |||
|---|---|---|---|
| Region | Asia | Business | janebloggs@yourcompany.com |
| Platform | Unix | Business | manager@yourcompany.com |
| Technical | joe.bloggs@technicians.com | ||
 Scan Information
Scan Information
|
|
|---|---|
| Scan Type | Enterprise |
| Started at | 13-Apr-15 11:54 |
| Finished at | 13-Apr-15 12:54 |
Ports: 5 (High:1 Low:4)
| Port | Protocol | Service | Details | ||
|---|---|---|---|---|---|
| 53 | tcp | domain | None | ||
| 53 | udp | dns | version.bind TXT "8.2.2-P6" | ||
| 161 | udp | snmp | uptime 347844596 centiseconds | ||

|
0 | icmp | echo reply | Response Received | |

|
14 | icmp | timestamp reply | Timestamp is 12:47:32 |
Ports Closed Since the Last Scan: 1 (High:1 Low:0)
| Port | Protocol | Service | Details | ||
|---|---|---|---|---|---|
| 23 | tcp | telnet | Response Received |
Vulnerabilities: 5 (High:3 Medium:1 Low:1)
| Vulnerability | 10605 | BIND < 8.2.3 Buffer Overrun

|
High Risk |
|---|
| Description | This system is running a vulnerable version of BIND, according to its banner. There is a buffer overrun vulnerability in code related to transaction signatures (TSIG). A remote attacker could use this to crash the service and take control of the system. | ||||
|---|---|---|---|---|---|
| Solution | Upgrade to an unaffected version, or apply a patch. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-2001-0010 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | |||
| CVE-2001-0011 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-2001-0012 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | ||||
| CVE-2001-0013 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| Deadline | 13 August 2014 | ||||
| First Found | 13 March 2015 | Port | 53/udp | Last 6 Assessments | 





|
| Vulnerability | 90027 | High Risk Ports Open | High Risk |
|---|
| Description | The following high risk ports are open: PORT SERVICE 161/udp snmp Note: Even if the ports are immediately closed after being opened, this is still a security risk as packets are reaching the destination host. It is recommended to completely drop packets from untrusted sources instead. |
||||
|---|---|---|---|---|---|
| Solution | Ensure that the ports are filtered by your router or firewall or close the ports on the affected systems. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 6.4 (Medium) (AV:N/AC:L/Au:N/C:P/I:P/A:N) | |||
| First Found | 13 October 2014 | Port | general | Last 6 Assessments | 





|
| Vulnerability | 10264 | SNMP Default Community Names | High Risk |
|---|
| Description | This system is running an SNMP agent which uses an easily guessable community string. This enables an attacker to extract a large amount of useful information. If a writeable community string is guessable, an attacker could make configuration changes to the server. Here is a sample of the information that can be extracted: host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.1 = "System Idle Process" host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.8 = "System" host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.168 = "SMSS.EXE" host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.192 = "CSRSS.EXE" host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.212 = "WINLOGON.EXE" host.hrSWRun.hrSWRunTable.hrSWRunEntry.hrSWRunName.240 = "SERVICES.EXE" |
||||
|---|---|---|---|---|---|
| Solution | Disable SNMP, or change the community string to something unguessable. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE References | CVE-1999-0186 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | |||
| CVE-1999-0254 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-1999-0516 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-1999-0517 | CVSS2 7.5 (High) (AV:N/AC:L/Au:N/C:P/I:P/A:P) | ||||
| CVE-2004-0311 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| CVE-2004-1474 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:N/I:P/A:N) | ||||
| CVE-2010-1574 | CVSS2 10.0 (High) (AV:N/AC:L/Au:N/C:C/I:C/A:C) | ||||
| First Found | 13 February 2015 | Port | 161/udp | Last 6 Assessments | 





|
| Vulnerability | 10595 | DNS Zone Transfer

|
Medium Risk |
|---|
| Description | This system is running a name server that allows DNS zone transfers to be performed. This information could be useful to an attacker trying to map your network. The configuration may be intentional, but it's usual practice to restrict zone transfers. Here is a sample of the data that can be extracted: mailer2.example.com. 10800 IN A 192.168.0.110 mailer3.example.com. 10800 IN A 192.168.0.111 mailer4.example.com. 10800 IN A 192.168.0.113 ntp0.example.com. 10800 IN A 192.168.0.114 |
||||
|---|---|---|---|---|---|
| Solution | Restrict zone transfers to trusted addresses, usually just your slave name servers | ||||
| Category | Hosting or infrastructure flaw. | ||||
| CVE Reference | CVE-1999-0532 | CVSS2 5.0 (Medium) (AV:N/AC:L/Au:N/C:P/I:N/A:N) | |||
| Deadline | 13 February 2015 | ||||
| First Found | 13 March 2015 | Port | 53/tcp | Last 6 Assessments | 





|
| Vulnerability | 90001 | Holes Detected in Firewall Configuration | Low Risk |
|---|
| Description | This system is protected by a firewall which blocks access to TCP ports in inconsistent ways. Incoming TCP connections to most ports are simply dropped, however some ports were discovered where the connection is actively refused, for example with a TCP RST. This often indicates a firewall configuration error, and commonly occurs when the configuration has not been altered in line with changing system configuration behind the firewall. For example when a service such as a mail server is removed, but the corresponding firewall rule is not. The TCP ports which actively refuse connections are: 443, 10000 |
||||
|---|---|---|---|---|---|
| Solution | Reconfigure your firewall to completely drop all connections on ports that you are not running services on. | ||||
| Category | Hosting or infrastructure flaw. | ||||
| References | Firewalls FAQ | ||||
| CVE Reference | CVE-MAP-NOMATCH | CVSS2 2.6 (Low) (AV:N/AC:H/Au:N/C:P/I:N/A:N) | |||
| First Found | 13 March 2015 | Port | general/tcp | Last 6 Assessments | 





|
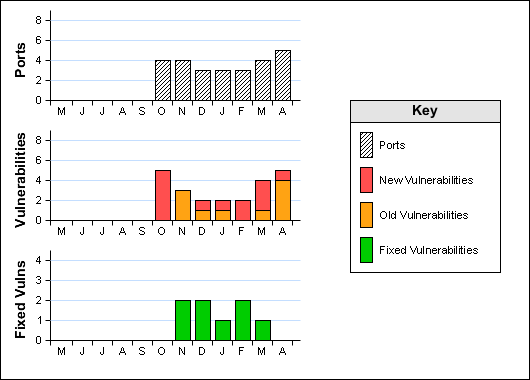
Historical Information